Instrukcja obsługi Hikvision DS-2CD2386G2-I(U)
Hikvision
Kamera monitorująca
DS-2CD2386G2-I(U)
Przeczytaj poniżej 📖 instrukcję obsługi w języku polskim dla Hikvision DS-2CD2386G2-I(U) (157 stron) w kategorii Kamera monitorująca. Ta instrukcja była pomocna dla 4 osób i została oceniona przez 2 użytkowników na średnio 4.5 gwiazdek
Strona 1/157

Network Camera User Manual
0
User Manual
UD18000B
Network Camera

Network Camera User Manual
1
User Manual
© 20 Hangzhou Hikvision Digital Technology Co., Ltd. All rights reserved. 20
This Manual is the property of Hangzhou Hikvision Digital Technology Co., Ltd. or its
aliates (hereinaer referred to as "Hikvision"), and it cannot be reproduced,
changed, translated, or distributed, parally or wholly, by any means, without the
prior wrien permission of Hikvision. Unless otherwise expressly stated herein,
Hikvision does not make any warranes, guarantees or representaons, express or
implied, regarding to the Manual, any informaon contained herein.
About this Manual
The Manual includes instrucons for using and managing the Product. Pictures, charts,
images and all other informaon hereinaer are for descripon and explanaon only.
The informaon contained in the Manual is subject to change, without noce, due to
rmware updates or other reasons. Please nd the latest version of this Manual at the
Hikvision website (hp://www.hikvision.com/).
Please use this Manual with the guidance and assistance of professionals trained in
supporng the Product.
Trademarks Acknowledgement
and other Hikvision’s trademarks and logos are the properes of
Hikvision in various jurisdicons.
Other trademarks and logos menoned are the properes of their respecve
owners.
The terms HDMI and HDMI High-Denion Mulmedia Interface, and the
HDMI Logo are trademarks or registered trademarks of HDMI Licensing
Administrator, Inc. in the United States and other countries.
LEGAL DISCLAIMER
TO THE MAXIMUM EXTENT PERMITTED BY APPLICABLE LAW, THIS MANUAL AND
Network Camera User Manual
2
THE PRODUCT DESCRIBED, WITH ITS HARDWARE, SOFTWARE AND FIRMWARE,
ARE PROVIDED "AS IS" AND "WITH ALL FAULTS AND ERRORS". HIKVISION MAKES
NO WARRANTIES, EXPRESS OR IMPLIED, INCLUDING WITHOUT LIMITATION,
MERCHANTABILITY, SATISFACTORY QUALITY, OR FITNESS FOR A PARTICULAR
PURPOSE. THE USE OF THE PRODUCT BY YOU IS AT YOUR OWN RISK. IN NO EVENT
WILL HIKVISION BE LIABLE TO YOU FOR ANY SPECIAL, CONSEQUENTIAL,
INCIDENTAL, OR INDIRECT DAMAGES, INCLUDING, AMONG OTHERS, DAMAGES
FOR LOSS OF BUSINESS PROFITS, BUSINESS INTERRUPTION, OR LOSS OF DATA,
CORRUPTION OF SYSTEMS, OR LOSS OF DOCUMENTATION, WHETHER BASED ON
BREACH OF CONTRACT, TORT (INCLUDING NEGLIGENCE), PRODUCT LIABILITY, OR
OTHERWISE, IN CONNECTION WITH THE USE OF THE PRODUCT, EVEN IF
HIKVISION HAS BEEN ADVISED OF THE POSSIBILITY OF SUCH DAMAGES OR LOSS.
YOU ACKNOWLEDGE THAT THE NATURE OF INTERNET PROVIDES FOR INHERENT
SECURITY RISKS, AND HIKVISION SHALL NOT TAKE ANY RESPONSIBILITIES FOR
ABNORMAL OPERATION, PRIVACY LEAKAGE OR OTHER DAMAGES RESULTING
FROM CYBER-ATTACK, HACKER ATTACK, VIRUS INSPECTION, OR OTHER INTERNET
SECURITY RISKS; HOWEVER, HIKVISION WILL PROVIDE TIMELY TECHNICAL
SUPPORT IF REQUIRED.
YOU AGREE TO USE THIS PRODUCT IN COMPLIANCE WITH ALL APPLICABLE LAWS,
AND YOU ARE SOLELY RESPONSIBLE FOR ENSURING THAT YOUR USE CONFORMS
TO THE APPLICABLE LAW. ESPECIALLY, YOU ARE RESPONSIBLE, FOR USING THIS
PRODUCT IN A MANNER THAT DOES NOT INFRINGE ON THE RIGHTS OF THIRD
PARTIES, INCLUDING WITHOUT LIMITATION, RIGHTS OF PUBLICITY,
INTELLECTUAL PROPERTY RIGHTS, OR DATA PROTECTION AND OTHER PRIVACY
RIGHTS. YOU SHALL NOT USE THIS PRODUCT FOR ANY PROHIBITED END-USES,
INCLUDING THE DEVELOPMENT OR PRODUCTION OF WEAPONS OF MASS
DESTRUCTION, THE DEVELOPMENT OR PRODUCTION OF CHEMICAL OR
BIOLOGICAL WEAPONS, ANY ACTIVITIES IN THE CONTEXT RELATED TO ANY
NUCLEAR EXPLOSIVE OR UNSAFE NUCLEAR FUEL-CYCLE, OR IN SUPPORT OF
HUMAN RIGHTS ABUSES.

Network Camera User Manual
3
IN THE EVENT OF ANY CONFLICTS BETWEEN THIS MANUAL AND THE APPLICABLE
LAW, THE LATER PREVAILS.
Safety Instrucon
These instrucons are intended to ensure that the user can use the product correctly
to avoid danger or property loss.
The precauon measure is divided into "Warnings" and "Cauons":
Warnings: Serious injury or death may be caused if any of these warnings are
neglected.
Cauons: Injury or equipment damage may be caused if any of these cauons are
neglected.
Warnings Follow these safeguards to
prevent serious injury or death.
Cauons Follow these precauons to
prevent potenal injury or material
damage.
Warnings:
If camera fails to synchronize local time with that of the network, you need to set
up camera me manually. Visit the camera and enter system sengs interface for
me seng.
Please adopt the power adapter which can meet the safety extra low voltage (SELV)
standard. And source with 12 V or 24 VDC AC (depending on models) according to
the IEC60950-1 and Limited Power Source standard.
To reduce the risk of fire or electrical shock, do not expose this product to rain or
moisture.
This installaon should be made by a qualied service person and should conform
to all the local codes.

Network Camera User Manual
4
Please install blackouts equipment into the power supply circuit for convenient
supply interrupon.
Please make sure that the ceiling can support more than 50(N) Newton gravies if
the camera is xed to the ceiling.
If the product does not work properly, please contact your dealer or the nearest
service center. Never aempt to disassemble the camera yourself. (We shall not
assume any responsibility for problems caused by unauthorized repair or
maintenance.)
Cauons:
Make sure the power supply voltage is correct before using the camera.
Do not drop the camera or subject it to physical shock.
Do not touch sensor modules with ngers. If cleaning is necessary, use a clean
cloth with a bit of ethanol and wipe it gently. If the camera will not be used for an
extended period of me, put on the lens cap to protect the sensor from dirt.
Do not aim the camera lens at the strong light such as sun or incandescent lamp.
The strong light can cause fatal damage to the camera.
The sensor may be burned out by a laser beam, so when any laser equipment is
being used, make sure that the surface of the sensor not be exposed to the laser
beam.
Do not place the camera in extremely hot, cold temperatures (refer to product
specicaon for working temperature), dusty or damp environment, and do not
expose it to high electromagnec radiaon.
To avoid heat accumulaon, ensure there is good venlaon to the device.
Keep the camera away from water and any liquids.
While shipping, pack the camera in its original, or equivalent, packing materials.
Or packing the same texture.
Improper use or replacement of the baery may result in hazard of explosion.
Please use the manufacturer recommended battery type.

Network Camera User Manual
5
Notes:
For the camera supports IR, you are required to pay aenon to the following
precauons to prevent IR reecon:
Dust or grease on the dome cover will cause IR reecon. Please do not remove
the dome cover lm unl the installaon is nished. If there is dust or grease on
the dome cover, clean the dome cover with clean so cloth and isopropyl alcohol.
Make certain the installaon locaon does not have reecve surfaces of objects
too close to the camera. The IR light from the camera may reect back into the
lens causing reection.
The foam ring around the lens must be seated ush against the inner surface of
the bubble to isolate the lens from the IR LEDS. Fasten the dome cover to camera
body so that the foam ring and the dome cover are attached seamlessly.
Network Camera User Manual
9
Conguring Cloud Storage................................................................................ 146
Playback .............................................................................................147
Picture ................................................................................................149
Appendix …………………………………………………………………………………………………. ……150
Appendix 1 SADP Software Introducon ...............................................................150
Appendix 2 Port Mapping ......................................................................................153
Appendix 3 …………………………………………………………………………………….………………… 155

Network Camera User Manual
10
System Requirement
Operang System
Microso Windows XP SP1 and above version
CPU
2.0 GHz or higher
RAM
1G or higher
Display
1024×768 resoluon or higher
Web Browser
For camera that supports plug-in free live view
Internet Explorer 8 – 11, Mozilla Firefox 30.0 and above version and Google
Chrome 41.0 and above version.
Note:
For Google Chrome 45 and its above version or Mozilla Firefox 52 and its above
version that are plug-in free, Picture Playback and funcons are hidden.
To use menoned funcons via web browser, change to their lower version, or
change to Internet Explorer 8.0 and above version.
For camera that does NOT support plug-in free live view
Internet Explorer 8 – 11, Mozilla Firefox 30.0 – 51, and Google Chrome 41.0 – .44

Network Camera User Manual
11
Network Connection
Note:
You shall acknowledge that the use of the product with Internet access might be
under network security risks. For avoidance of any network attacks and
information leakage, please strengthen your own protection. If the product does
not work properly, please contact with your dealer or the nearest service center.
To ensure the network security of the network camera, we recommend you to
have the network camera assessed and maintained termly. You can contact us if
you need such service.
Before you start:
If you want to set the network camera via a LAN (Local Area Network), please refer
to 2.1 Setting the Network Camera over the LAN .
If you want to set the network camera via WAN (Wide Area Network), please a
refer to 2.2 Setting the Network Camera over the WAN .
Setting the Network Camera over the LAN
Purpose:
To view and configure the camera via a LAN, you need to connect the network camera
in the same subnet with your computer, and install the SADP or iVMS-4200 software
to search and change the IP of the network camera.
Note: For the detailed introduction of SADP, please refer to Appendix 1 SADP Software
Introduction.
2.1.1 Wiring over the LAN
The following figures show the two ways of cable connection of network camera and a
a computer:
Purpose:

Network Camera User Manual
12
To test the network camera, you can directly connect the network camera to the
computer with a network cable as shown in Figure 2-1.
Refer to the Figure 2-2 to set network camera over the LAN via a switch or a router.
Network Cable
or
Network Camera
Computer
Connecting Directly
Network Cable
Network Cable
or
or
Network Camera Computer
Connecting via a Switch or Routera
2.1.2 Activating the Camera
You are required to activate the camera first by setting a strong password for it before
you can use the camera.
Activation via Web Browser, Activation via SADP, and Activation via Client Software are
all supported.
Activation via Web Browser
Steps:
1. Power on the camera, and connect the camera to the network.
2. Input the IP address into the address bar of the web browser, and click Enter to
enter the activation interface.
Notes:
The default IP address of the camera is 192.168.1.64.
The computer and the camera should belong to the same subnet.
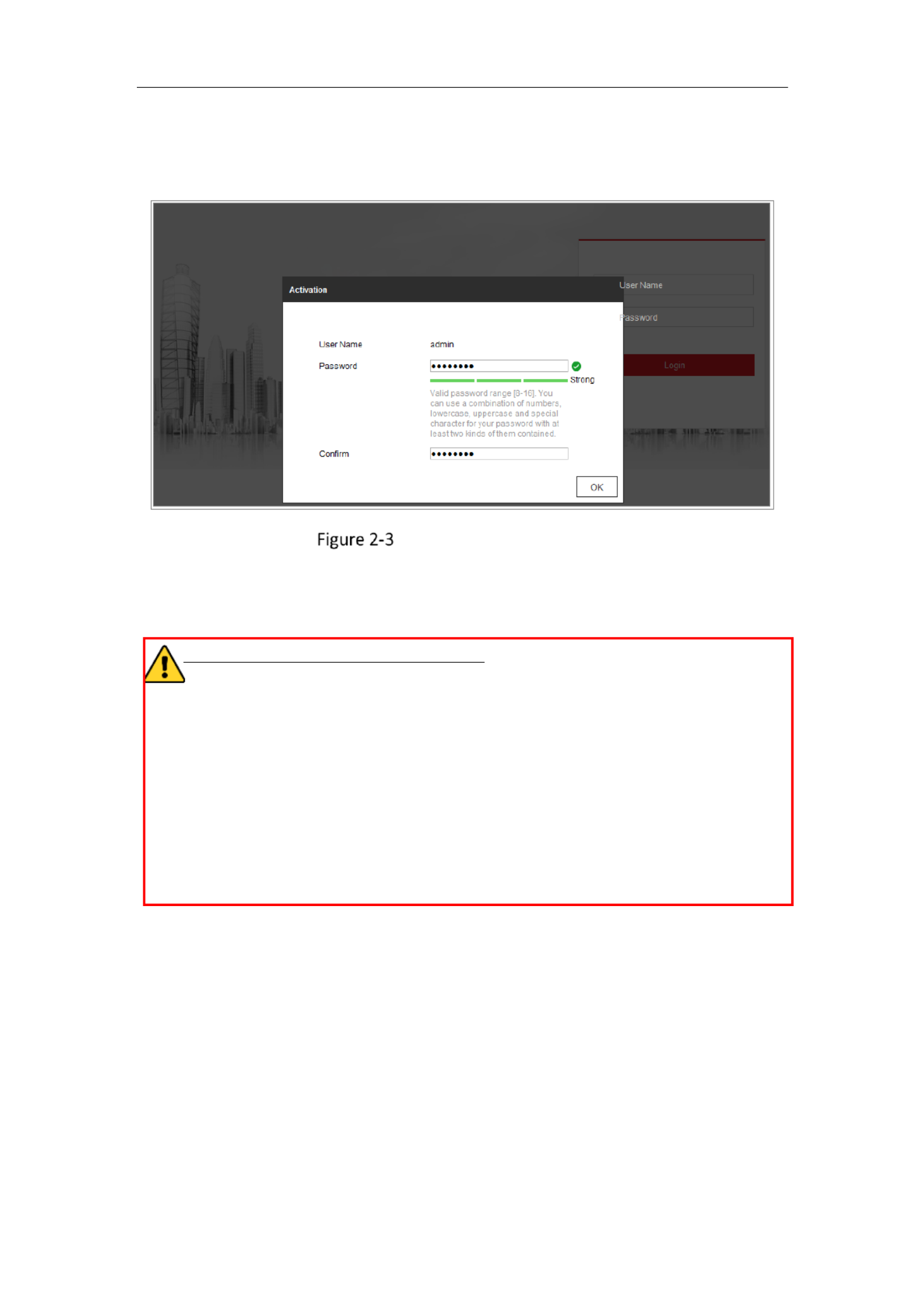
Network Camera User Manual
13
For the camera enables the DHCP by default, you need to use the SADP software to
search the IP address.
Activation via Web Browser
3. Create and input a password into the password field.
A password with user name in it is not allowed.
STRONG PASSWORD RECOMMENDED–We highly recommend you create a
strong password of your own choosing (using a minimum of 8 characters,
including at least three of the following categories: upper case letters, lower case
letters, numbers, and special characters) in order to increase the security of your
product. And we recommend you reset your password regularly, especially in the
high security system, resetting the password monthly or weekly can better
protect your product.
4. Confirm the password.
5. Click OK to save the password and enter the live view interface.
Activation via SADP Software
SADP software is used for detecting the online device, activating the camera, and
resetting the password.
Get the SADP software from the supplied disk or the official website, and install the
SADP according to the prompts. Follow the steps to activate the camera.

Network Camera User Manual
14
Steps:
1. Run the SADP software to search the online devices.
2. Check the device status from the device list, and select the inactive device.
SADP Interface
Note:
The SADP software supports activating the camera in batch. Refer to the user manual
of SADP software for details.
3. Create and input the password in the password field, and confirm the password.
A password with user name in it is not allowed.
STRONG PASSWORD RECOMMENDED– We highly recommend you
create a strong password of your own choosing (using a minimum of 8
characters, including at least three of the following categories: upper
case letters, lower case letters, numbers, and special characters) in order
to increase the security of your product. And we recommend you reset
your password regularly, especially in the high security system, resetting
the password monthly or weekly can better protect your product.
Note:
You can enable the Hik-Connect service for the device during activation.
Select inactive device.
Input and confirm
password.

Network Camera User Manual
15
4. Click Activate to start activation.
You can check whether the activation is completed on the popup window. If activation
failed, please make sure that the password meets the requirement and try again.
5. Change the device IP address to the same subnet with your computer by either
modifying the IP address manually or checking the checkbox of Enable DHCP.
Modify the IP Address
6. Input the admin password and click to activate your IP address Modify
modification.
The batch IP address modification is supported by the SADP. Refer to the user manual
of SADP for details.
Activation via Client Software
The client software is versatile video management software for multiple kinds of
devices.
Get the client software from the supplied disk or the official website, and install the
software according to the prompts. Follow the steps to activate the camera.

Network Camera User Manual
16
Steps:
1. Run the client software and the control panel of the software pops up, as shown
in the figure below.
Control Panel
2. Click the icon to enter the Device Management interface, as Device Management
shown in the figure below.
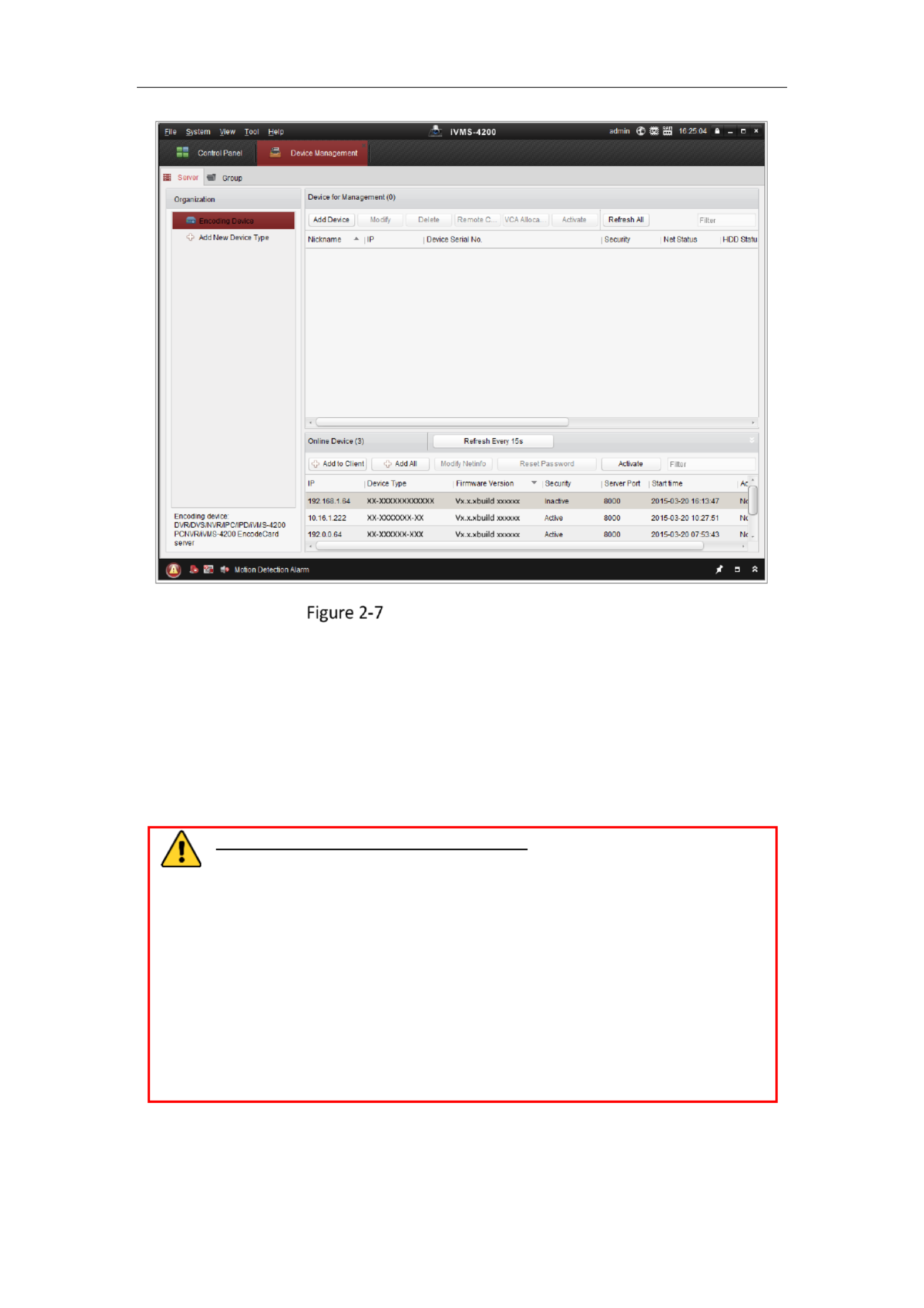
Network Camera User Manual
17
Device Management Interface
3. Check the device status from the device list, and select an inactive device.
4. Click the Activate button to pop up the Activation interface.
5. Create a password and input the password in the password field, and confirm the
password.
A password with user name in it is not allowed.
STRONG PASSWORD RECOMMENDED–We highly recommend you
create a strong password of your own choosing (using a minimum of 8
characters, including at least three of the following categories: upper case
letters, lower case letters, numbers, and special characters) in order to
increase the security of your product. We recommend you reset your
password regularly, especially in the high security system, resetting the
password monthly or weekly can better protect your product.

Network Camera User Manual
18
Activation Interface (Client Software)
6. Click OK button to start activation.
7. Click the Modify Netinfo button to pop up the Network Parameter Modification
interface, as shown in the figure below.
Modifying the Network Parameters
8. Change the device IP address to the same subnet with your computer by either
modifying the IP address manually or checking the checkbox of Enable DHCP.
9. Input the password to activate your IP address modification.

Network Camera User Manual
19
2.1.3 (Optional) Setting Security Question
Security question is used to reset the admin password when admin user forgets the
password.
Admin user can follow the pop-up window to complete security question settings
during camera activation. Or, admin user can go to interface to set User Management
up the function.
Setting the Network Camera over the WAN
Purpose:
This section explains how to connect the network camera to the WAN with a static IP
or a dynamic IP.
Static IP Connection
Before you start:
Please apply a static IP from an ISP (Internet Service Provider). With the static IP
address, you can connect the network camera via a router or connect it to the WAN
directly.
Connecting the network camera via a router
Steps:
1. Connect the network camera to the router.
2. Assign a LAN IP address, the subnet mask and the gateway. Refer to 2.1.2 Activating
the Camera for detailed IP address configuration of the network camera.
3. Save the static IP in the router.
4. Set port mapping, e.g 80, 8000, and 554 ports. ., The steps for port mapping vary
according to the different routers. Please call the router manufacturer for
assistance with port mapping.
Note: Refer to Appendix 2 Port Mapping for detailed information about port mapping.

Network Camera User Manual
20
5. Visit the network camera through a web browser or the client software over the
internet.
Accessing the Camera through Router with Static IP
Connecting the network camera with static IP directly
You can also save the static IP in the camera and directly connect it to the internet
without using a router. Refer to 2.1.2 Activating the Camera for detailed IP address
configuration of the network camera.
Accessing the Camera with Static IP Directly
2.2.2 Dynamic IP Connection
Before you start:
Please apply a dynamic IP from an ISP. With the dynamic IP address, you can connect
the network camera to a modem or a router.
Connecting the network camera via a router
Steps:
1. Connect the network camera to the router.
2. In the camera, assign a LAN IP address, the subnet mask and the gateway. Refer to
2.1.2 Activating the Camera for detailed IP address configuration of the network
camera.
3. In the router, set the PPPoE user name, password and confirm the password.
4. Set port mapping. E.g. 80, 8000, and 554 ports. The steps for port mapping vary

Network Camera User Manual
21
depending on different routers. Please call the router manufacturer for assistance
with port mapping.
Note: Refer to Appendix 2 Port Mapping for detailed information about port mapping.
5. Apply a domain name from a domain name provider.
6. Configure the DDNS settings in the setting interface of the router.
7. Visit the camera via the applied domain name.
Connecting the network camera via a modem
Purpose:
This camera supports the PPPoE auto dial-up function. The camera gets a public IP
address by ADSL dial-up after the camera is connected to a modem. You need to
configure the PPPoE parameters of the network camera. Refer to 7.1.3 Configuring
PPPoE Settings for detailed configuration.
Accessing the Camera with Dynamic IP
Note: The obtained IP address is dynamically assigned via PPPoE, so the IP address
always changes after rebooting the camera. To solve the inconvenience of the dynamic
IP, you need to get a domain name from the DDNS provider (E.g. DynDns.com). Please
follow the steps below for normal domain name resolution and private domain name
resolution to solve the problem.
Normal Domain Name Resolution
Normal Domain Name Resolution

Network Camera User Manual
22
Steps:
1. Apply a domain name from a domain name provider.
2. Configure the DDNS settings in the DDNS Settings interface of the network camera.
Refer to 7.1.2 Configuring DDNS Settings for detailed configuration.
3. Visit the camera via the applied domain name.

Network Camera User Manual
23
Access to the Network
Camera
Accessing by Web Browsers
Note:
For certain camera models, HTTPS is enabled by default and the camera creates an
unsigned certificate automatically. When you access to the camera the first time, the
web browser prompts a notification about the certificate issue.
To cancel the notification, install a signed-certificate to the camera. For detailed
operation, see 7.2.6 HTTPS Settings.
Steps:
1. Open the web browser.
2. In the browser address bar, input the IP address of the network camera, and press
the Enter key to enter the login interface.
Note:
The default IP address is 192.168.1.64. You are recommended to change the IP
address to the same subnet with your computer.
3. Input the user name and password and click . Login
The admin user should configure the device accounts and user/operator permissions
properly. Delete the unnecessary accounts and user/operator permissions.
Note:
The IP address locked if the admin/user/operator performs 7 failed password is
attempts.

Network Camera User Manual
24
Login Interface
4. Click . Login
5. (Optional) Install the plug-in before viewing the live video and operating the
camera. Follow the installation prompts to install the plug- in
Note:
For camera that supports plug-in free live view, if you are using Google Chrome 57
and its above version or Mozilla Firefox 52 and its above version, plug-in installation
is not required. But Picture Playback and functions are hidden. To use mentioned
function via web browser, change to their lower version, or change to Internet
Explorer 8.0 and above version.
Accessing by Client Software
The product CD contains the iVMS-4200 client software You can view the live video .
and manage the camera with the software.
Follow the installation prompts to install the software. The control panel and live view
interface of iVMS-4200 client software are shown as below.
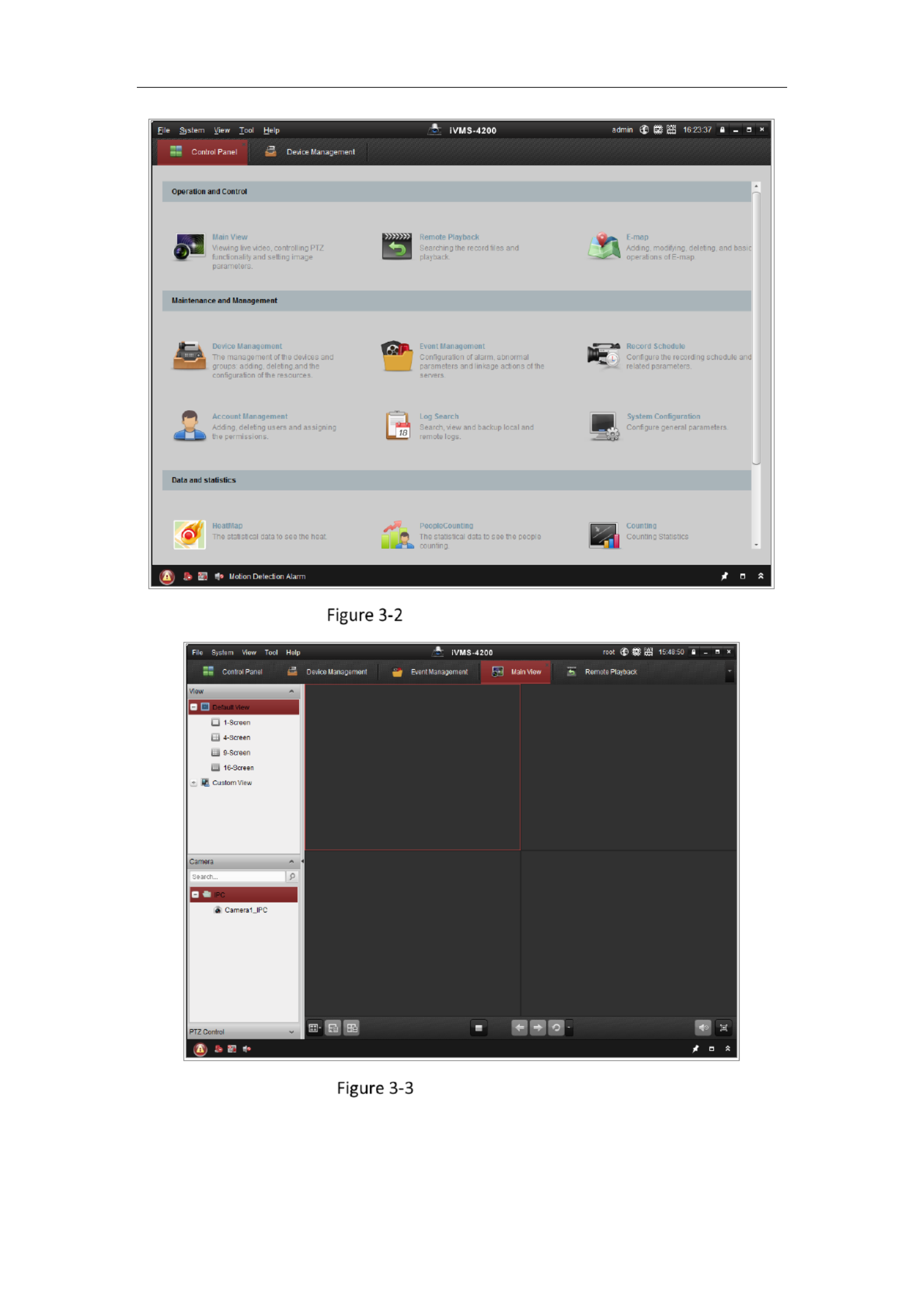
Network Camera User Manual
25
iVMS-4200 Control Panel
iVMS-4200 Main View

Network Camera User Manual
26
Wi-Fi Settings
Purpose:
By connecting to the wireless network, you do not need to use cable of any kind for
network connection, which is very convenient for the actual surveillance application.
Note: This chapter is only applicable for the cameras with the built-in Wi-Fi module.
Configuring Wi-Fi Connection in Manage and Ad-hoc
Modes
Purpose:
Two connection modes are supported. Choose a mode as desired and perform the
steps to configure the Wi-Fi.
Wireless Connection in Manage Mode
Steps:
1. Enter the Wi-Fi configuration interface.
Configuration> Network> Advanced Settings> -Wi Fi
2. Click Search to search the online wireless connections.
Wi-Fi List

Network Camera User Manual
27
3. Click to choose a wireless connection on the list.
Wi-Fi Setting- Manage Mode
4. Check the radio button to select the Network mode Manage,as and the
Security mode of the network is automatically shown when you select the
wireless network, please do not change it manually.
Note: These parameters are exactly identical with those of the router.
5. Enter the key to connect the wireless network. The key should be that of the
wireless network connection you set on the router.
Wireless Connection in Ad-hoc Mode
If you choose the Ad-hoc mode, you do not need to connect the wireless camera via
a router. The scenario is the same as you connect the camera and the PC directly
with a network cable.
Steps:
1. Choose Ad-hoc mode.
Wi-Fi Setting- -hocAd

Network Camera User Manual
28
2. Customize a SSID for the camera.
3. Choose the Security Mode of the wireless connection.
4. Enable the wireless connection function for your PC.
5. On the PC side, search the network and you can see the SSID of the camera
listed.
Ad-hoc Connection Point
6. Choose the SSID and connect.
Security Mode Description:
Security Mode
You can choose the Security Mode as not-encrypted, WEP, WPA-personal, WPA-
enterprise, WPA2-personal, and WPA2-enterprise.
WEP mode:

Network Camera User Manual
30
TLS or EAP-PEAP.
EAP-TLS
EAP-TLS
Identity - Enter the user ID to present to the network.
Private key password – Enter the password for your user ID.
EAPOL version - Select the version used (1 or 2) in your access point.
CA Certificates - Upload a CA certificate to present to the access point for
authentication.
EAP-PEAP:
User Name - Enter the user name to present to the network
Password - Enter the password of the network
PEAP Version - Select the PEAP version used at the access point.
Label - Select the label used by the access point.
EAPOL version - Select version (1 or 2) depending on the version used at the access
point.
CA Certificates - Upload a CA certificate to present to the access point for
authentication.
For your privacy and to better protect your system against security risks, we
strongly recommend the use of strong passwords for all functions and network

Network Camera User Manual
31
devices. The password should be something of your own choosing (using a
minimum of 8 characters, including at least three of the following categories:
upper case leers, lower case leers, numbers and special characters) in order to
increase the security of your product.
Proper conguraon of all passwords and other security sengs is the
responsibility of the installer and/or end-user.
Easy Wi-Fi Connection with WPS function
Purpose:
The setng of the wireless network connecon is never easy. To avoid the complex
seng of the wireless connecon you can enable the WPS funcon.
WPS (Wi-Fi Protected Setup) refers to the easy conguraon of the encrypted
connecon between the device and the wireless router. The WPS makes it easy to
add new devices to an exisng network without entering long passphrases. There are
two modes of the WPS connecon, the PBC mode and the PIN mode.
Note: If you enable the WPS funcon, you do not need to congure the parameters
such as the encrypon type and you do not need to know the key of the wireless
connecon.
Steps:
Wi-Fi Sengs - WPS
PBC : Mode

Network Camera User Manual
32
PBC refers to the Push-Button-Configuration, in which the user simply has to push a
button, either an actual or virtual one (as the button on the
configuration interface of the IE browser), on both the Access Point (and a registrar
of the network) and the new wireless client device.
1. Check the checkbox of to enable WPS.
2. Choose the connection mode as PBC.
Note: Support of this mode is mandatory for both the Access Points and the
connecting devices.
3. Check on the Wi-Fi router to see if there is a WPS button. If yes, push the button
and you can see the indicator near the button start flashing, which means the WPS
function of the router is enabled. For detailed operation, please see the user guide of
the router.
4. Push the WPS button to enable the function on the camera.
If there is not a WPS button on the camera, you can also click the virtual button to
enable the PBC function on the web interface.
5. Click Connect button.
When the PBC mode is both enabled in the router and the camera, the camera and
the wireless network is connected automatically.
PIN Mode:
The PIN mode requires a Personal Identification Number (PIN) to be read from either
a sticker or the display on the new wireless device. This PIN must then be entered to
connect the network, usually the Access Point of the network.
Steps:
1. Choose a wireless connection on the list and the SSID is loaded automatically.
2. Choose Use route PIN code.

Network Camera User Manual
33
Use PIN Code
If the PIN code is generated from the router side, you should enter the PIN code you
get from the router side in the Router PIN code eld.
3. Click Connect.
Or
You can generate the PIN code on the camera side. And the expired me for the PIN
code is 120 seconds.
1. Click Generate.
2. Enter the code to the router, in the example, enter 48167581 to the router.
IP Property Settings for Wireless Network
Connection
The default IP address of wireless network interface controller is 192.168.1.64. When
you connect to the wireless network, you can change the default IP.
Steps:
1. Enter the TCP/IP conguration interface.
Configuration Network Basic Settings > > > TCP/IP
2. Select the Wlan tab.

Network Camera User Manual
34
Setting WLAN Parameters
3. Customize the IPv4 address, the IPv4 Subnet Mask and the Default Gateway.
The setting procedure is the same with that of LAN.
If you want to be assigned the IP address, you can check the checkbox to enable
the DHCP.
Network Camera User Manual
37
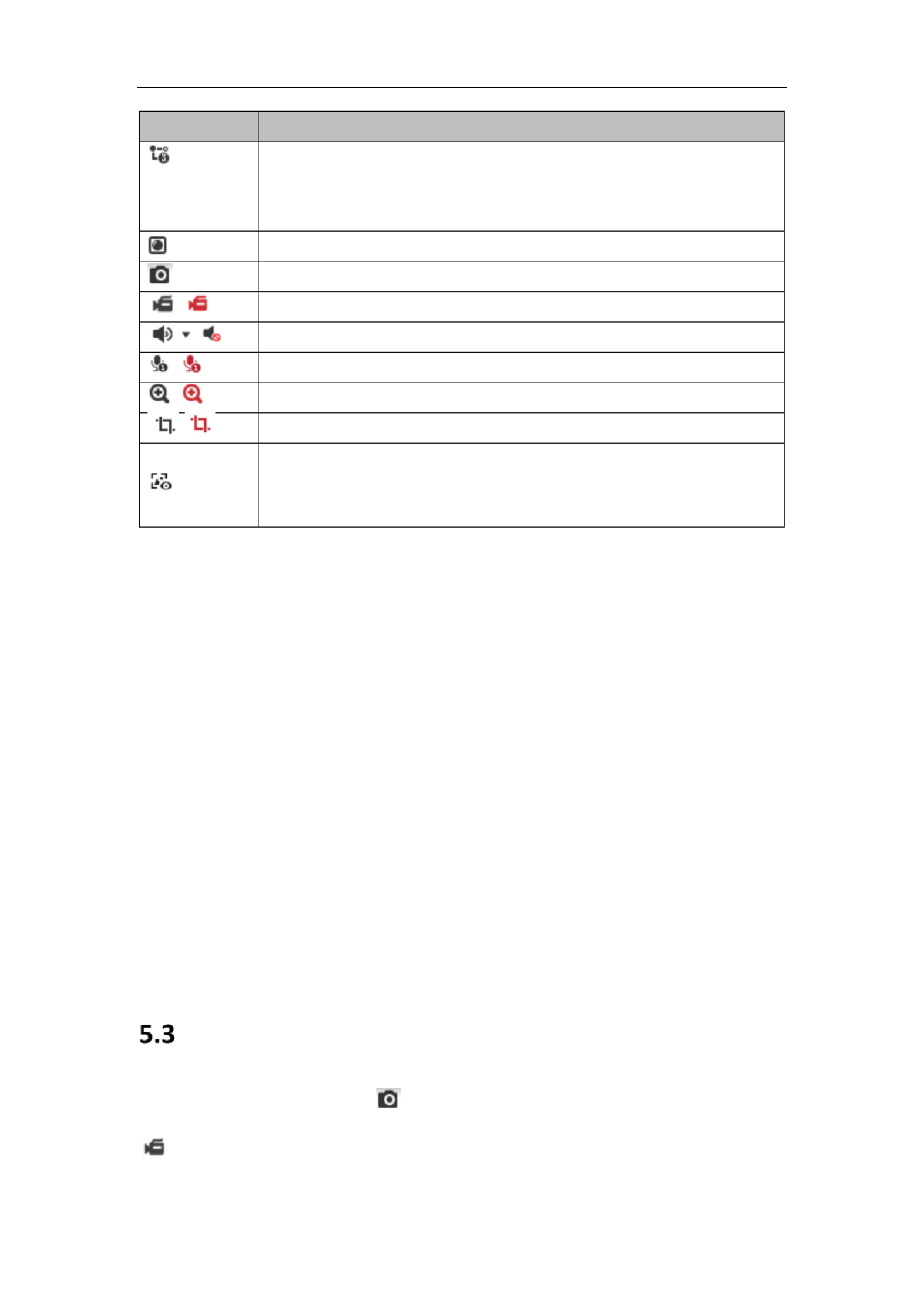
Icon
Descripon
, etc.
Supported video streams vary according to camera models.
For the camera models that support 10 streams, go to
Video/Audio > Custom to add the streams.
Click to select the third-party plug-in.
Manually capture the picture.
/
Manually start/stop recording.
/
Audio on and adjust volume /Mute.
/
Turn on/o microphone.
/
Start/stop digital zoom funcon.
/
Start/stop pixel counter
Click the buon to display pictures captured by camera.
Note: The funcon is only available for certain camera models that
support face capture.
Note: The icons vary according to the dierent camera models.
Pixel Counter:
Steps:
1. Click Start Pixel Counter to enable the funcon.
2. Drag the mouse on the image to select the desired rectangle area. The width pixel
and height pixel is displayed on the boom of the web.
3. Click the buon again to stop the function.
Note:
The pixel counter is only supported under the main stream and only one rectangle is
supported.
Full-screen Mode:
You can double-click on the live video to switch the current live view into full-
screen or return to normal mode from the full-screen.
Recording and Capturing Pictures Manually
In the live view interface, click on the toolbar to capture the live pictures or click
to record the live view. The saving paths the captured pictures and clips can be of

Network Camera User Manual
39
PTZ Control Panel
Click the zoom/focus/iris buttons to realize lens control.
Notes:
There are eight direction arrows ( ) in the control , , , , , , ,
panel. Click the arrows to realize adjustment in the relave posions.
For the cameras that support lens movements only, the direction buons are
invalid.
Descripons of PTZ Control Panel
Icon
Descripon
Zoom in/out
Focus near/far
Iris /+ -
PTZ speed adjustment
Light on/o
Wiper on/o
Auxiliary focus
Inialize lens
Adjust speed of pan/lt movements
Start Manual Tracking
Start 3D Zoom
5.5.2 Setng/Calling a Preset
Seng a Preset:
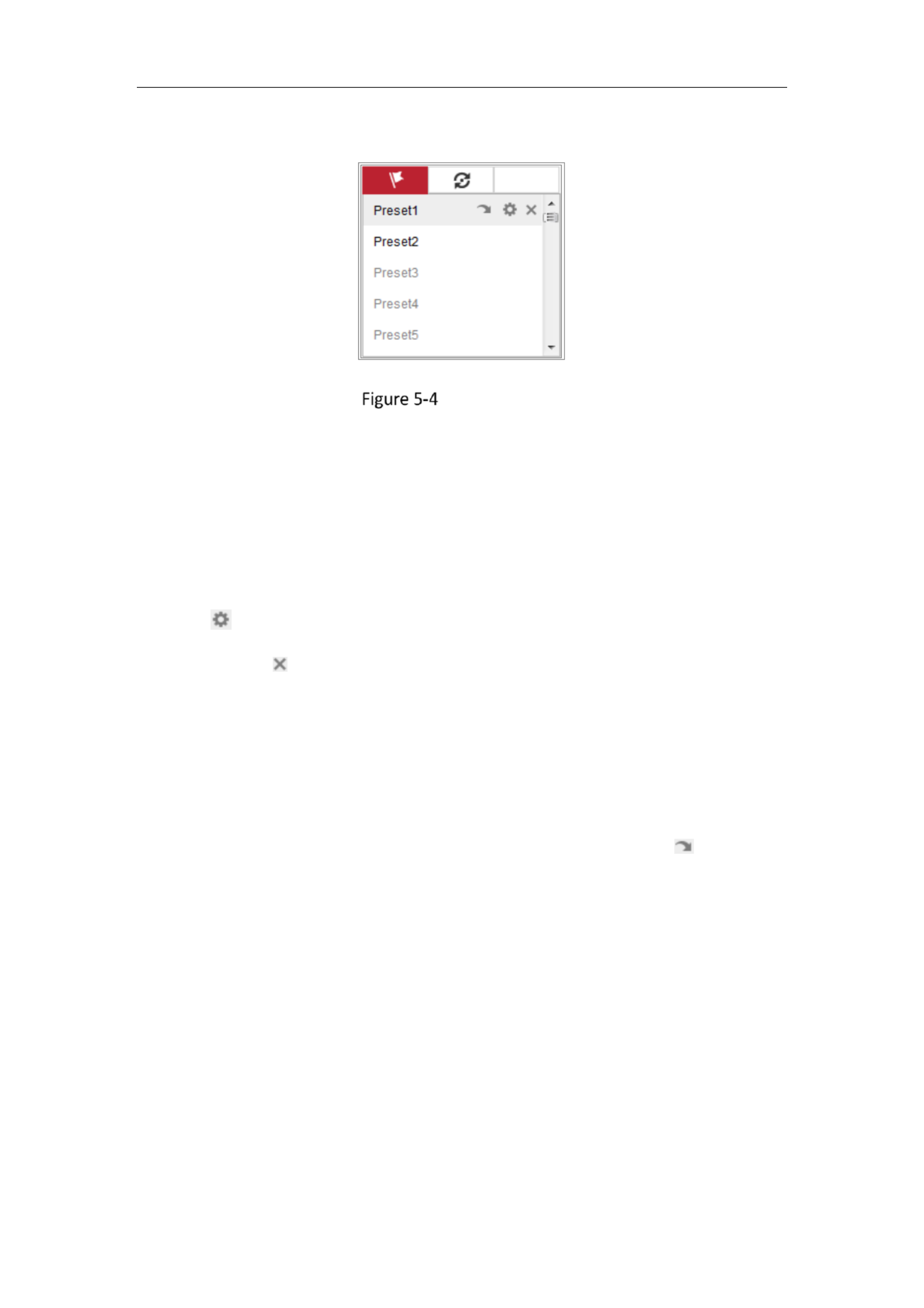
Network Camera User Manual
40
1. In the PTZ control panel, select a preset number from the preset list.
Setting a Preset
2. Use the PTZ control buons to move the lens to the desired posion.
• Pan the camera to the right or left.
• Tilt the camera up or down.
• Zoom in or out.
• Refocus the lens.
3. Click to nish the seng of the current preset.
4. You can click to delete the preset.
Calling a Preset:
This feature enables the camera to point to a specified preset scene manually or
automatically when an event takes place.
For the defined preset, you can call it at any time to the desired preset scene.
In the PTZ control panel, select a defined preset from the list and click to call the
preset.
Or you can place the mouse on the presets interface, and call the preset by typing
the preset No. to call the corresponding presets.

Network Camera User Manual
41
Calling a Preset
5.5.3 Setng/Calling a Patrol
Note:
No less than 2 presets should be congured before you set a patrol.
Steps:
1. Click to enter the patrol conguraon interface.
2. Select a path No., and click to add the congured presets.
3. Select the preset, and input the patrol duraon and patrol speed.
4. Click OK to save the rst preset.
5. Follow the steps above to add the other presets.
Add Patrol Path
6. Click OK to save a patrol.
7. Click to start the patrol, and click to stop it.
8. (Oponal) Click to delete a patrol.

Network Camera User Manual
42
Install Plug-in
Certain operaon system and web browser may restrict the display and operaon of
the camera funcon. You should install plug-in or complete certain sengs to ensure
normal display and operaon.
Operaon
System
Web Browser
Operaon
Windows
Internet Explorer 8+
Follow pop-up prompts to
complete plug-in installaon.
Google Chrome 57+
Mozilla Firefox 52+
Click to download
and install plug-in.
Mac OS
Google Chrome 57+
Mozilla Firefox 52+
Mac Safari 16+
Plug-in installaon is not
required.
Enable WebSocket or
WebSockets (Conguraon >
Network > Advanced
Setngs > Network Service)
for normal live view.
Display and operaon of certain
funcons are restricted. For
example, Playback and Picture are
not available. For detailed
restricted funcon, refer to the
actual devic e.
Note:
The camera only supports Windows and Mac OS system and do not support Linux es
system.

Network Camera User Manual
44
and the face detecon is enabled as well, when a face is detected, it will be
marked with a green rectangle on the live view.
Display POS Informaon: Enable the funcon, feature informaon of the
detected target is dynamically displayed near the target in the live image.
The feature informaon of dierent funcons dierent. For example, and is ID
waing me for Queue Management, height for People Counng, etc.
Note:
Display POS Informaon is only available for certain camera models.
Image Format: Choose the image format for picture capture.
Live View Parameters
Record File Sengs: Set the saving path of the recorded video les. Valid for the
record les you recorded with the web browser.
Record File Size: Select the packed size of the manually recorded and
downloaded video les to 256M, 512M or 1G. Aer the selecon, the
maximum record le size is the value you selected.
Save record les to: Set the saving path for the manually recorded video les.
Save downloaded les to: Set the saving path for the downloaded video les
in playback mode.
Picture and Clip Sengs: Set the saving paths of the captured pictures and clipped
video les. Valid for the pictures you capture with the web browser.
Save snapshots in live view to: Set the saving path of the manually captured
pictures in live view mode.
Save snapshots when playback to: Set the saving path of the captured
pictures in playback mode.
Save clips to: Set the saving path of the clipped video les in playback mode.

Network Camera User Manual
45
Note: You can click Browse to change the directory for saving the clips and pictures,
and click to open the set folder of clips and picture saving. Open
3. Click Save to save the sengs.
Congure System Setngs
Purpose:
Follow the instrucons below to configure the system setngs, include System Sengs,
Maintenance, Security, and User Management etc.,
6.2.1 Conguring Basic Informaon
Enter the Device Informaon interface: Conguraon System System Seings > > >
Basic Informaon.
In the Basic Informaon interface, you can edit the Device Name and Device No.
Other information of the network camera, such as Model, Serial No., Firmware Version,
Encoding Version, Number of Channels, Number of HDDs, Number of Alarm Input and
Number of Alarm Output are displayed. The informaon cannot be changed in this
menu. It is the reference for maintenance or modicaon in future.
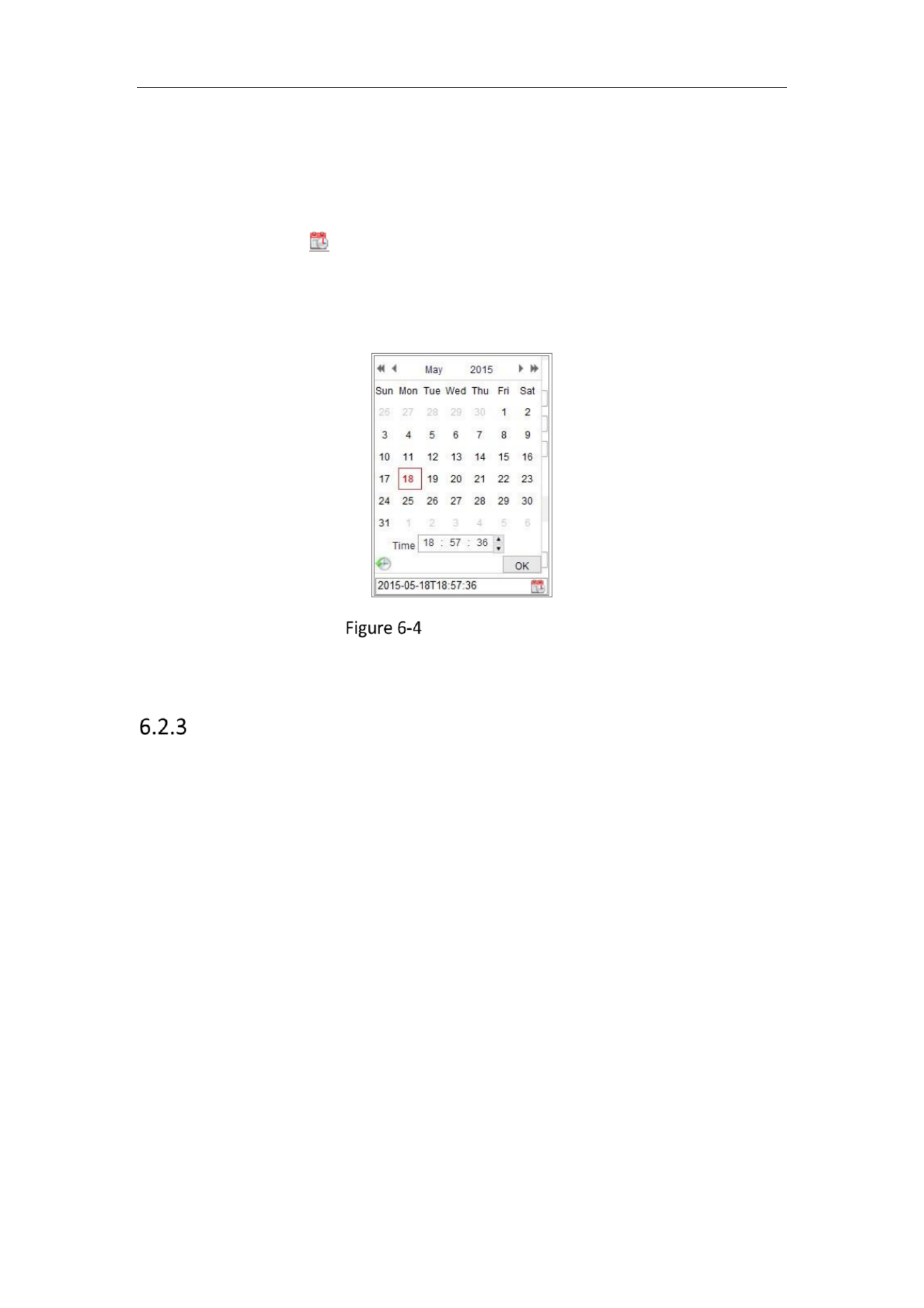
6.2.2 Conguring Time Sengs
Purpose:
You can follow the instructions in this secon to congure the time synchronizaon
and DST sengs.
Steps:
1. Enter the Time Sengs interface, Conguraon > System> System Sengs > Time
Setngs.

Network Camera User Manual
46
Time Setngs
2. Select the Time Zone of your locaon from the drop-down menu.
3. Congure the NTP sengs.
(1) Click to enable the funcon. NTP
(2) Congure the following sengs:
Server Address: IP address of NTP server.
NTP Port: Port of NTP server.
Interval: The me interval between the two synchronizing acons with NTP
server.
(3) (Oponal) You can click the Test buon to test the me synchronizaon
funcon via NTP server.
Time Sync by NTP Server
Note: If the camera is connected to a public network, you should use a NTP server that
has a me synchronizaon funcon, such as the server at the Naonal Time Center (IP
Address: 210.72.145.44). If the camera is set in a customized network, NTP soware
can be used to establish a NTP server for me synchronizaon.
Network Camera User Manual
47
Congure the manual me synchronizaon.
(1) Check the to enable the manual me synchronizaon Manual Time Sync.
funcon.
(2) Click the icon to select the date, me from the pop-up calendar.
(3) (Oponal) You can check Sync. with computer me item to synchronize the
me of the device with that of the local PC.
Time Sync Manually
Click Save to save the setngs.
Conguring DST Setngs
Purpose:
Daylight Saving Time (DST) is a way of making beer use of the natural daylight by
seng your clock forward one hour during the summer months, and back again in the
fall.
Congure the DST according to your actual demand.
Steps:
1. Enter the DST conguraon interface: Conguraon > System > System Setngs >
DST.

Network Camera User Manual
48
DST Sengs
2. Select the start me and the end me.
3. Select the DST Bias.
4. Click Save to acvate the sengs.
6.2.4 Conguring RS-232 Sengs
The RS-232 port can be used in two ways:
Console: Connect a computer to the camera through the serial port. Device
parameters can be congured by using soware such as HyperTerminal. The serial
port parameters must be the same as the serial port parameters of the camera.
Transparent Channel: Connect a serial device directly to the camera. The serial
device will be controlled remotely by the computer through the network.
Steps:
1. Enter RS-232 Port Seng interface: Conguraon > System System Seings > >
RS-232.
2. Congure the Baud Rate, Data Bit, Stop Bit, Parity, Flow Control, and Usage.
RS-232 Settings
Note: If you want to connect the camera by the RS-232 port, the parameters of the RS-

Network Camera User Manual
49
232 should be the same with the parameters you congured here.
3. Click Save to save the setngs.
Conguring RS-485 Sengs
Purpose:
The RS-485 serial port is used to control the PTZ of the camera. The conguring of the
PTZ parameters should be done before you control the PTZ unit.
Note: Only certain camera models support this funcon.
Steps:
1. Enter RS-485 Port Seng interface: Conguraon System System Setngs> > >
RS-485.
RS-485 Setngs
2. Set the RS-485 parameters and click to save the sengs.Save
By default, the Baud Rate is set as 9600 bps, the Data Bit is 8, the stop bit is 1 and
the Parity and Flow Control is None.
Note: The Baud Rate, PTZ Protocol and PTZ Address parameters should be exactly the
same as the PTZ camera parameters.
6.2.6 Conguring VCA Resource
Purpose:
VCA resource oers you opons to enable certain VCA funcons according to actual
need when several VCA funcons are available. It helps allocate more resources to the
desired funcons.

Network Camera User Manual
50
Steps:
1. Enter VCA Resource conguraon interface:
Configuration > System > System Settings > VCA Resource
2. Select a desired VCA combinaon. Available VCA combinaon varies according to
dierent camera models.
3. Click Save to save the sengs. A reboot is required aer seng the VCA Resource.
Notes:
• VCA combinaons are mutually exclusive. When you acvate one combinaon,
the others are hidden.
• Only certain camera models support the funcon.
6.2.7 Configuring Metadata Settings
Purpose:
Metadata is the raw data the camera collects before algorithm processing. Metadata
of intrusion detecon, line crossing detecon, region entrance detecon, region
exing detection, unattended baggage detecon, object removal, queue
management and face capture can be uploaded. If enabled, the metadata of the
corresponding event are available for users to explore the possibility of various data
usage.
Steps:
1. Enter Metadata sengs interface:
Configuration > System > System Settings > metadata Settings
2. Check the checkbox of the corresponding funcon to enable the metadata
funcon.
The metadata of the smart event includes the target ID, target coordinate and time
informaon.
The metadata of face capture includes the rule information, target ID, target
coordinate, face grading and me informaon. The camera detects the whole
image by default. If the region is congured in the face capture sengs, the
camera detects the congured region.

Network Camera User Manual
51
3. Check Enable Stream Rule to overlay the stream rule on the live view image. Make
sure you have checked and selected the Sub-stream Sub-stream in the live view.
4. Check Overlay Rule Frame and Target Frame on Background Picture to enable the
function. Make sure you have checked Sub-stream and selected the Sub-stream in
the live view.
Note: Only certain camera models support the function.
6.2.8 Open Source Software License
Information about the open source software that applies to the IP camera can be
checked if required. Go to Configuration > System Settings > About.
Maintenance
Upgrade & Maintenance
Purpose:
The upgrade & maintenance interface allows you to process the operations, including
reboot, partly restore, restore to default, export/import the configuration files, and
upgrade the device.
Enter the Maintenance interface: Configuration > System Maintenance Upgrade > >
& Maintenance.
Reboot: Restart the device.
Restore: Reset all the parameters except the IP parameters and user information
to the default settings.
Default: Restore all the parameters to the factory default.
Notes:
• After restoring the default settings, the IP address is also restored to the
default IP address, please be careful for this action.
• For camera that supports Wi-Fi, wireless dial, or wlan function, Restore action
does not restore the related settings of mentioned functions to default.

Network Camera User Manual
52
• When you restore the device to the factory default, video standard is reserved.
Information Export
Device Parameters: click to export the current configuration file of the camera.
This operation requires admin password to proceed.
For the exported file, you also have to create an encryption password. The
encryption password is required when you import the file to other cameras.
Diagnose Information: click to download log and system information.
Import Config. File
Configuration file is used for the batch configuration of the camera s.
Steps:
1. Click Browse to select the saved configuration file.
2. Click Import and input the encryption password that you set during exporting.
Note: You need to reboot the camera after importing configuration file.
Upgrade: Upgrade the device to a certain version.
Steps:
1. Select firmware or firmware directory to locate the upgrade file.
Firmware: Locate the exact path of the upgrade file.
Firmware Directory: Only the directory the upgrade file belongs to is required.
2. Click to select the local upgrade file and then click to start Browse Upgrade
remote upgrade.
Note: e upgrading process will take 1 to 10 minutes. Please do not disconnect Th
power of the camera during the process, and the camera reboots automatically
after upgrade.
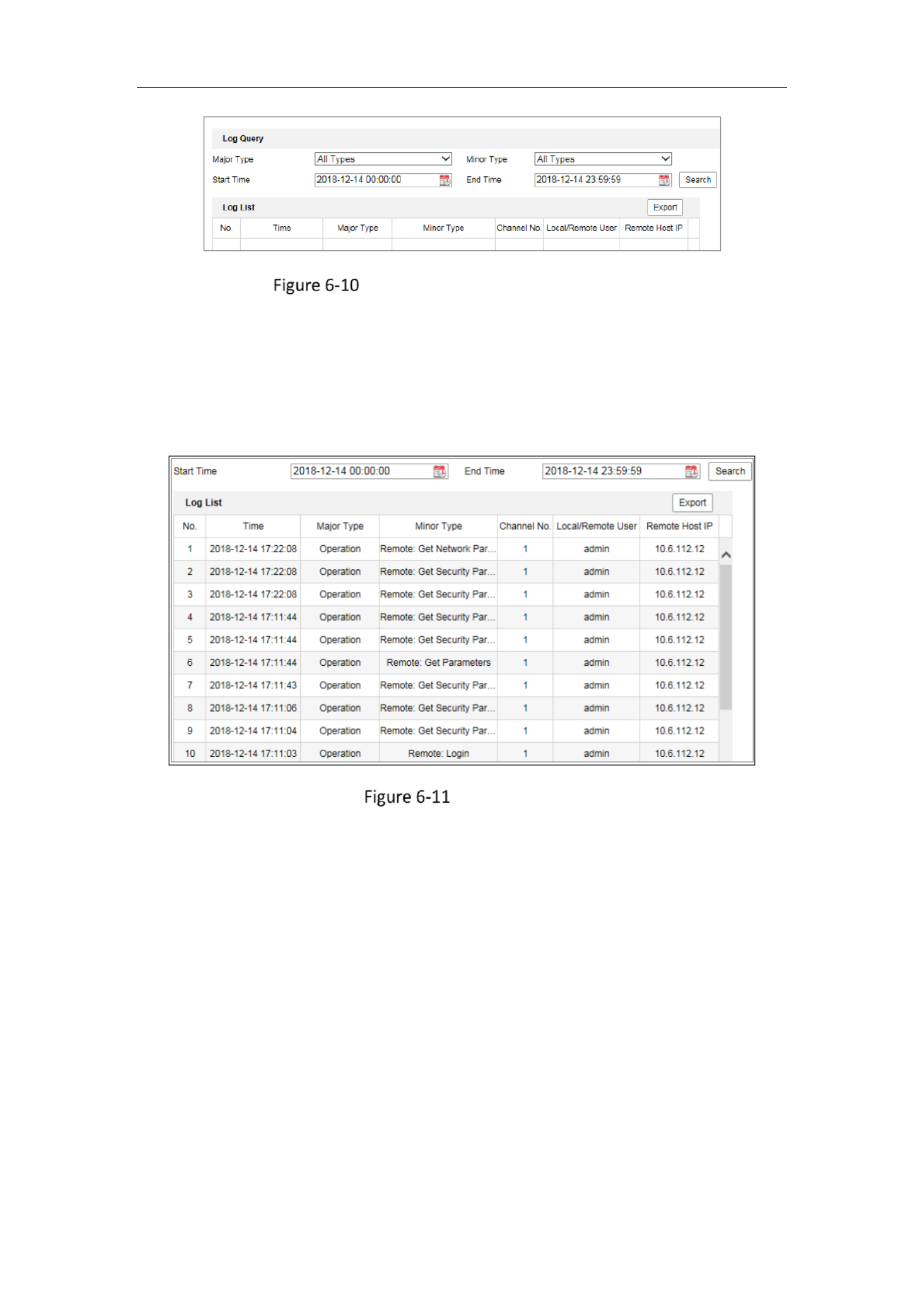
6.3.2 Log
Purpose:
The operation, alarm, exception and information of the camera can be stored in log
files. You can also export the log files on your demand.
Before you start:

Network Camera User Manual
53
Please configure network storage for the camera or insert a SD card in the camera.
Steps:
1. Enter log searching interface: Configuration System Maintenance Log > > > .
Log Searching Interface
2. Set the log search conditions to specify the search, including the Major Type, Minor
Type, Start Time and End Time.
3. Click to search log files. The matched log files will be displayed on the log Search
list interface.
Log Searching
4. To export the log files, click to save the log files.Export

Network Camera User Manual
54
6.3.3 System Service
Purpose:
System service settings refer to the hardware service the camera supports. Supported
functions vary according to the different cameras. For the cameras support IR Light,
ABF (Auto Back Focus), Auto Defog, or Status LED, you can select to enable or disable
the corresponding service according to the actual demands.
Note: Only certain device models support this function.
ABF: When ABF function is enabled, you can click on PTZ control panel to realize
auxiliary focus.
Third Stream: For some models, third stream is not enabled by default. Check Enable
Third Stream enable the function.to
eMMC Protection If you enable eMMC protection, the lifespan of the eMMC is :
displayed.
Enable Motion Detection: Check Enable Motion Detection to enable the function.
6.3.4 Security Audit Log
Purpose:
The security audit logs refer to the security operation logs. You can search and analyze
the security log files of the camera so that to find out the illegal intrusion and
troubleshooting the security events. Security audit logs can be saved on device flash.
The log will be saved every half hour after device booting.
Due to limited saving space of the flash, you can also save the logs on a log server.
Configure the server settings at Advanced Settings.
Note: Only certain camera models support the function.
Searching Logs
Steps:
1. Enter log searching interface: Configuration System Maintenance Security > > >
Audit Log.
Network Camera User Manual
55
Security Audit Log Searching Interface
2. Set the log search condions to specify the search, including the Major Type, Minor
Type, Start Time and End Time.
3. Click to search log les. The matched log les will be displayed on the log Search
list interface.
Log Searching
4. To export the log les, click to save the log les.Export
Setting Log Server
Steps:
1. Check Enable Log Upload Server.
2. Input Log Server IP and Log Server Port.
3. Click Test to test sengs.
4. Install cercates. Client cerficate and CA cercate are required.
• Client Certificate
(1) Click Create button to create the cercate request. Fill in the required
informaon in the popup window.
(2) Click Download to download the cercate request and submit it to the
Network Camera User Manual
56
trusted certificate authority for signature.
(3) Install the signed certificate to the device.
• CA Certificate
Install the CA certificate to the device.
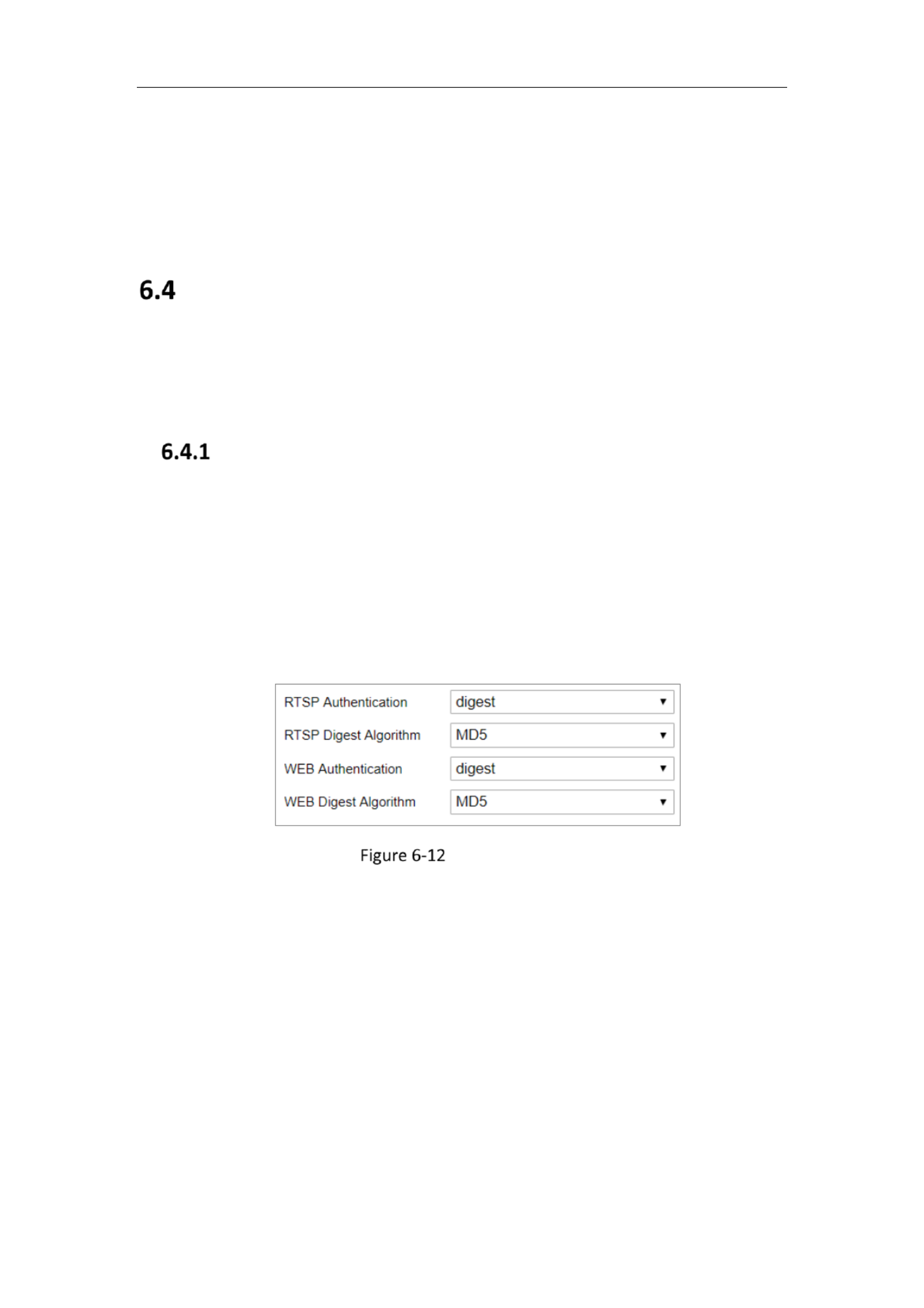
Security Settings
Configure the parameters, including Authentication, IP Address Filter, and Security
Service from security interface.
Authentication
Purpose:
You can specifically secure the stream data of live view.
Steps:
1. Enter the Authentication interface: Configuration > System Security> >
Authentication.
Authentication
2. Set up authentication method for RTSP authentication and WEB authentication,
RTSP digest algorithm, and WEB digest algorithm.
RTSP Authentication
Digest and digest/basic are supported, which means authentication information
is needed when RTSP request is sent to the device. If you select digest/basic, it
means the device supports digest or basic authentication. If you select digest,
the device only supports digest authentication.
RTSP Digest Algorithm
MD5, SHA256 and MD5/SHA256 encrypted algorithm in RTSP authentication. If

Network Camera User Manual
57
you enable the digest algorithm except for MD5, the third-party platform might
not be able to log in to the device or enable live view because of compatibility.
The encrypted algorithm with high strength is recommended.
WEB Authentication
Digest and digest/basic are supported, which means authentication information
is needed when WEB request is sent to the device. If you select digest/basic, it
means the device supports digest or basic authentication. If you select digest,
the device only supports digest authentication.
WEB Digest Algorithm
MD5, SHA256 and MD5/SHA256 encrypted algorithm in WEB authentication. If
you enable the digest algorithm except for MD5, the third-party platform might
not be able to log in to the device or enable live view because of compatibility.
The encrypted algorithm with high strength is recommended.
Note:
Refer to the specific content of protocol to view authentication requirements.
3. Click Save to save the settings.
6.4.2 IP Address Filter
Purpose:
This function makes it possible for access control.
Steps:
1. Enter the IP Address Filter interface: Configuration System Security IP > > >
Address Filter

Network Camera User Manual
58
IP Address Filter Interface
2. Check the checkbox of Enable IP Address Filter.
3. Select the type of IP Address Filter in the drop-down list, and Forbidden Allowed
are selectable.
4. Set the IP Address Filter list.
Add an IP Address
Steps:
(4) Click the Add to add an IP.
(5) Input the IP Adreess.
Add an IP
(6) Click the OK to finish adding.
Modify an IP Address
Steps:
(1) Left-click an IP address from filter list and click .Modify
(2) Modify the IP address in the text filed.
Modify an IP
(3) Click the OK to finish modifying.
Delete an IP Address or IP Addresses.
Select the IP address(es) and click Delete.

Network Camera User Manual
59
5. Click Save to save the settings.
6.4.3 Security Service
To enable the remote login, and improve the data communication security, the camera
provides the security service for better user experience.
Note: Only certain camera models support the function.
Steps:
1. Enter the security service configuration interface: Configuration > System >
Security Security Service > .
Security Service
2. Check the checkbox of Enable Illegal Login Lock.
Illegal Login Lock: it is used to limit the user login attempts. Login attempt from the
IP address is rejected if admin user performs 7 failed user name/password
attempts (5 times for the operator/user).
Note: If the IP address is rejected, you can try to login the device after 30 minutes.
Advanced Security
Purpose:
Advanced security offers options to manage more network security settings of the
device.
Security Reinforce
Check the checkbox to enable the function. Security reinforce is a solution to
enhance network security. With the function enabled, risky functions, protocols,
ports of the device are disabled and more secured alternative functions, protocols
and ports are enabled.
Control Timeout Settings

Network Camera User Manual
61
1. Click Add to add a user.
2. Input the Admin Password User Name Level Password., , select and input
Notes:
● Up to 31 user accounts can be created.
● Users of different levels own different default permissions. Operator and
user are selectable.
STRONG PASSWORD RECOMMENDED–We highly recommend you create
a strong password of your own choosing (using a minimum of 8 characters,
including at least three of the following categories: upper case letters, lower
case letters, numbers, and special characters) in order to increase the
security of your product. And we recommend you reset your password
regularly, especially in the high security system, resetting the password
monthly or weekly can better protect your product.
3. You can check or uncheck the permissions for the new user.
4. Click to finish the user addition.OK
Modifying a User
Steps:
1. Left-click to select the user from the list and click Modify.
2. Modify the and User Name, Level Password.
STRONG PASSWORD RECOMMENDED–We highly recommend you create a
strong password of your own choosing (using a minimum of 8 characters,
including at least three of the following categories: upper case letters, lower
case letters, numbers, and special characters) in order to increase the security
of your product. And we recommend you reset your password regularly,
especially in the high security system, resetting the password monthly or
weekly can better protect your product.
3. You can check or uncheck the permissions.
4. Click to finish the user modification.OK
Deleting a User

Network Camera User Manual
62
Steps:
1. Click to select the user you want to delete and click Delete.
2. Click OK on the pop-up dialogue box to confirm the deletion.
Setting Simultaneous Login
Steps:
1. Click General.
2. Slide the slide bar to set the simultaneous login. If the number of the illegal
login attempts exceeds the set threshold, your access will be denied.
As Operator or User
Operator or user can modify password. Old password is required for this action.
6.5.2 Security Question
Purpose:
Security question is used to recover the admin password when admin user forgets the
password. Recovering the password via the security questions and via the email are
available.
Note: Only certain camera models support the function.
Set Account Security:
You can set the security questions during camera activation. Or you can set the
function at user management interface.
Security question setting is not cleared when you restore the camera (not to default).
Steps:
1. Enter setting interface:
Configuration > System > User Management > User Management
2. Click Account Security Settings.
3. Select questions and input answers.
4. Enter the E-mail address to receive the verification code for password recovery.
5. Click OK to save the settings.
Reset Admin Password:

Network Camera User Manual
63
Before you start:
The PC used to reset password and the camera should belong to the same IP address
segment of the same LAN.
Steps:
1. Enter login interface via web browser.
2. Click Forget Password.
3. Select the verification mode to E-mail Verification.
4. Read the Privacy Policy and click .OK
5. Click Export QR Code and save the code to local.
6. Send the code to pw_recovery@hikvision.com as an attachment. Your email
account for password recovery will receive a verification code in 5 minutes.
Note:
The verification code is valid within 48 hours.
7. Input the verification code in the text field below.
Reset Password
8. Click Next.
9. Input the password and confirm.
10. Follow the instructions to create new password.a

Network Camera User Manual
64
Note:
User IP address is locked for 30 minutes after 7 failed attempts of answering
security questions.
Only certain camera models support the function.
Online Users
Purpose:
You can see the current users who are visiting the device through this interface. User
information, such as user name, level, IP address, and operation time, is displayed in
the User List.
Click Refresh to refresh the list.
View the Online Users
Network Camera User Manual
66
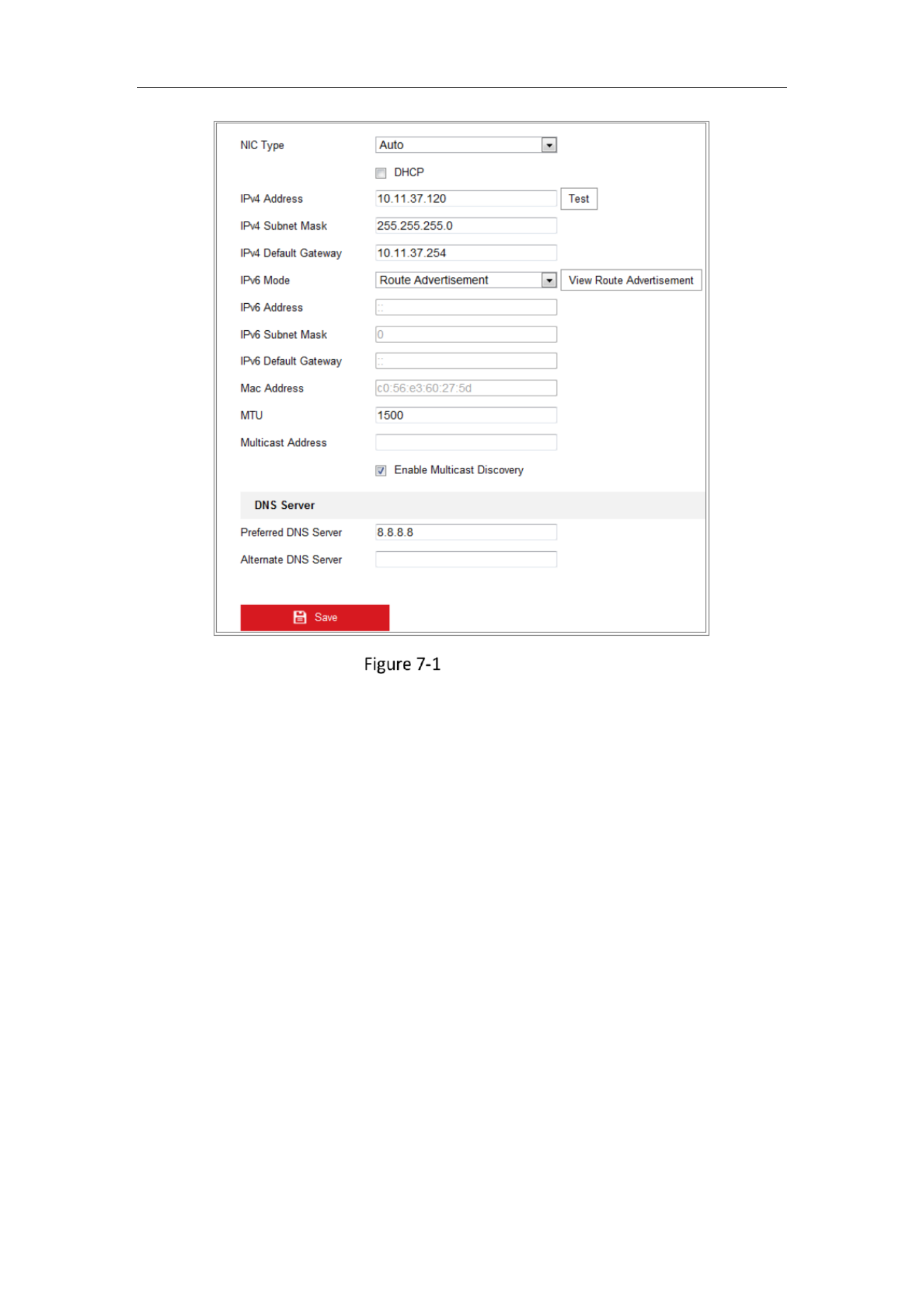
TCP/IP Settings
2. Configure the basic network settings, including the NIC Type, IPv4 or IPv6 Address,
IPv4 or IPv6 Subnet Mask, IPv4 or IPv6 Default Gateway, MTU settings and
Multicast Address.
3. (Optional) Check the checkbox of , and then the online Enable Multicast Discovery
network camera can be automatically detected by client software via private
multicast protocol in the LAN.
4. Configure the DNS server. Input the preferred DNS server, and alternate DNS
server.
5. Click Save to save the above settings.
Notes:
The valid value range of MTU is 1280 1500. to
The Multicast sends a stream to the multicast group address and allows multiple
clients to acquire the stream at the same time by requesting a copy from the
multicast group address. Before utilizing this function, you have to enable the

Network Camera User Manual
67
Multicast function of your router.
A reboot is required for the settings to take effect.
7.1.2 Configuring DDNS Settings
Purpose:
If your camera is set to use PPPoE as its default network connection, you can use the
Dynamic DNS (DDNS) for network access.
Before you start:
Registration on the DDNS server is required before configuring the DDNS settings of
the camera.
Steps:
1. Enter the DDNS Settings interface: Configuration > Network > Basic Settings >
DDNS.
2. Check the checkbox to enable this feature. Enable DDNS
3. Select DDNS Type. Two DDNS types are selectable: DynDNS and NO-IP.
DynDNS:
Steps:
(1) Enter of DynDNS (e.g. members.dyndns.org). Server Address
(2) In the text field, enter the domain name obtained from the DynDNS Domain
website.
(3) Enter the and registered on the DynDNS website. User Name Password
(4) Click Save to save the settings.

Network Camera User Manual
70
2. Set the ports of the camera.
HTTP Port: The default port number is 80, and it can be changed to any port No.
that is not occupied.
RTSP Port: The default port number is 554 and it can be changed to any port No.
ranges from 1 to 65535.
HTTPS Port: The default port number is 443, and it can be changed to any port No.
that is not occupied.
Server Port: The default server port number is 8000, and it can be changed to any
port No. ranges from 2000 to 65535.
Enhanced SDK Service Port: The default server number is 8443. It refers to the
port through which the client adds the device. Certificate verification is required
to ensure the secure access.
Note:
When you use client software to visit the camera and you have changed the server
port number, you have to input the correct server port number in login interface
to access to the camera.
WebSocket Port: The default port number is 7681. It can be changed to any port
No. ranges from 1 to 65535.
WebSockets Port: The default server port number is 7682. It can be changed to
any port No. ranges from 1 to 65535.
Note:
WebSocket and WebSockets protocol are used for plug-in free live view. For
detailed information, see 7.2.11.
3. Click Save to save the settings.
7.1.5 Configure NAT (Network Address Translation) Settings
Purpose:
NAT interface allows you to configure the UPnP™ parameters.
Universal Plug and Play (UPnP™) is a networking architecture that provides

Network Camera User Manual
71
compatibility among networking equipment, software and other hardware devices.
The UPnP protocol allows devices to connect seamlessly and to simplify the
implementation of networks in the home and corporate environments.
With the function enabled, you do not need to configure the port mapping for each
port, and the camera is connected to the Wide Area Network via the router.
UPnP Settings
Steps:
1. Enter the NAT settings interface. Configuration > Network > Basic Settings >
NAT.
2. Check the checkbox to enable the UPnP™ function.
Note:
Only when the UPnP™ function is enabled, ports of the camera are active.
3. Choose a friendly name for the camera, or you can use the default name.
4. Select the port mapping mode. Manual and Auto are selectable.
Note:
If you select Auto, you should enable UPnP™ function on the router.
If you select Manual, you can customize the value of the external port and
complete port mapping settings on router manually.
5. Click Save to save the settings.
Configuring Multicast
Purpose:

Network Camera User Manual
73
etc., by following the instructions in this section.
Configuring SNMP Settings
Purpose:
You can set the SNMP function to get camera status, parameters and alarm related
information, and manage the camera remotely when it is connected to the network.
Before you start:
Before setting the SNMP, please download the SNMP software and manage to receive
the camera information via SNMP port. By setting the Trap Address, the camera can
send the alarm event and exception messages to the surveillance center.
Note: The SNMP version you select should be the same as that of the SNMP software.
And you also need to use the different version according to the security level you
required. SNMP v1 provides no security and SNMP v2 requires password for access.
And SNMP v3 provides encryption and if you use the third version, HTTPS protocol
must be enabled.
For your privacy and to better protect your system against security risks, we
strongly recommend the use of strong passwords for all functions and network
devices. The password should be something of your own choosing (using a
minimum of 8 characters, including at least three of the following categories:
upper case letters, lower case letters, numbers and special characters) in order to
increase the security of your product.
Proper configuration of all passwords and other security settings is the
responsibility of the installer and/or end-user.
Steps:
1. Enter the SNMP Settings interface: Configuration > Network > Advanced
Settings > SNMP.

Network Camera User Manual
74
SNMP Settings
2. Check to enable the feature Enable SNMPv1, Enable SNMP v2c, Enable SNMPv3
correspondingly.
3. Configure the SNMP settings.
Note: The settings of the SNMP software should be the same as the settings you
configure here.

Network Camera User Manual
75
4. Click to save and finish the settings. Save
Note:
To lower the risk of information leakage, you are suggested to enable SNMP v3 instead
of SNMP v1 or v2.
7.2.2 Configuring FTP Settings
Purpose:
You can configure the FTP/SFTP server related information to enable the uploading of
the captured pictures to the FTP/SFTP server. The captured pictures can be triggered
by events or a timing snapshot task.
Steps:
1. Enter the FTP Settings interface: Configuration > Network > Advanced Settings >
FTP.
FTP Settings
2. Select the FTP protocol.
3. Input the server address and port.
4. Configure the FTP/SFTP settings; and the user name and password are required
for the server login.

Network Camera User Manual
76
For your privacy and to better protect your system against security risks, we
strongly recommend the use of strong passwords for all functions and network
devices. The password should be something of your own choosing (using a
minimum of 8 characters, including at least three of the following categories:
upper case letters, lower case letters, numbers and special characters) in order
to increase the security of your product.
Proper configuration of all passwords and other security settings is the
responsibility of the installer and/or end-user.
5. Set the directory structure and picture filing interval.
Directory Directory Structure: In the field, you can select the root directory,
parent directory and child directory. When the parent directory is selected, you
have the option to use the Device Name, Device Number or Device IP for the name
of the directory; and when the Child Directory is selected, you can use the Camera
Name or Camera No. as the name of the directory.
Picture Filing Interval: For better picture management, you can set the picture
filing interval from 1 day to 30 days. Pictures captured in the same time interval
will be saved in one folder named after the beginning date and ending date of the
time interval.
Picture Name: Set the naming rule for captured picture files. You can choose
Default in the drop-down list to use the default rule, that is,
IP address_channel number_capture time_event type.jpg
(e.g., 10.11.37.189_01_20150917094425492_FACE_DETECTION.jpg).
Or you can customize it by adding a Custom Prefix to the default naming rule.
6. Check the Upload Picture checkbox to enable the function.
Upload Picture: To enable uploading the captured picture to the FTP server.
Anonymous Access to the FTP Server (in which case the user name and password
will not be required.): Check the Anonymous checkbox to enable the anonymous
access to the FTP server.

Network Camera User Manual
99
2. Check Enable Target Cropping checkbox to enable the funcon.
3. Set Third Stream as the stream type.
4. Select the cropping resoluon for the video display of target area. A red rectangle
is displayed on the live video to mark the target area, and you can click-and-drag
the rectangle to locate the target area as desired.
5. Click Save to save the setngs.

Network Camera User Manual
101
The refers to the electronic shuer time, which ranges from 1 Exposure Time to
1/100,000s. Adjust it according to the actual luminance condion.
Gain of image can also be manually congured from 0 to 100. The bigger the value
is, the brighter would the image be, and the noise would be amplied to a larger
extent.
Exposure Sengs
Focus
For camera support motor-driven lens, you can set the focus mode as Auto,
Manual or Semi-auto.
Auto: Camera focus is adjusted automacally according to the actual monitoring
scenario.
Manual: You can control the lens by adjusng the zoom, focus, lens inialization,
and auxiliary focus manually.
Semi-Auto: Camera will focus automacally when you adjust the zoom
parameters.
Day/Night Switch
Select the Day/Night Switch mode according to dierent surveillance demand.
Day, Night, Auto, Scheduled-Switch, and Triggered by alarm input are selectable
for day/night switch.
Day/Night Switch
Day: the camera stays at day mode.
Specyfikacje produktu
| Marka: | Hikvision |
| Kategoria: | Kamera monitorująca |
| Model: | DS-2CD2386G2-I(U) |
Potrzebujesz pomocy?
Jeśli potrzebujesz pomocy z Hikvision DS-2CD2386G2-I(U), zadaj pytanie poniżej, a inni użytkownicy Ci odpowiedzą
Instrukcje Kamera monitorująca Hikvision

12 Stycznia 2025

12 Stycznia 2025

12 Stycznia 2025

12 Stycznia 2025

11 Stycznia 2025

7 Stycznia 2025

19 Grudnia 2024

19 Grudnia 2024

19 Grudnia 2024

19 Grudnia 2024
Instrukcje Kamera monitorująca
- Kamera monitorująca Sony
- Kamera monitorująca Samsung
- Kamera monitorująca Tenda
- Kamera monitorująca Motorola
- Kamera monitorująca Stabo
- Kamera monitorująca Logitech
- Kamera monitorująca Xiaomi
- Kamera monitorująca Braun
- Kamera monitorująca Pioneer
- Kamera monitorująca TP-Link
- Kamera monitorująca Philips
- Kamera monitorująca Bosch
- Kamera monitorująca Gigaset
- Kamera monitorująca EZVIZ
- Kamera monitorująca Conceptronic
- Kamera monitorująca Panasonic
- Kamera monitorująca Canon
- Kamera monitorująca Crestron
- Kamera monitorująca Withings
- Kamera monitorująca Asus
- Kamera monitorująca Nedis
- Kamera monitorująca AG Neovo
- Kamera monitorująca Reolink
- Kamera monitorująca Boss
- Kamera monitorująca TRENDnet
- Kamera monitorująca Marquant
- Kamera monitorująca Toshiba
- Kamera monitorująca D-Link
- Kamera monitorująca August
- Kamera monitorująca Niceboy
- Kamera monitorująca Ring
- Kamera monitorująca Garmin
- Kamera monitorująca Imou
- Kamera monitorująca Blaupunkt
- Kamera monitorująca Grundig
- Kamera monitorująca APC
- Kamera monitorująca Honeywell
- Kamera monitorująca BLOW
- Kamera monitorująca Manhattan
- Kamera monitorująca Strong
- Kamera monitorująca Swann
- Kamera monitorująca Kwikset
- Kamera monitorująca Kodak
- Kamera monitorująca Cisco
- Kamera monitorująca ORNO
- Kamera monitorująca Broan
- Kamera monitorująca Moxa
- Kamera monitorująca Synology
- Kamera monitorująca Gembird
- Kamera monitorująca ZTE
- Kamera monitorująca Turing
- Kamera monitorująca Lindy
- Kamera monitorująca Minox
- Kamera monitorująca Zebra
- Kamera monitorująca DSC
- Kamera monitorująca JVC
- Kamera monitorująca ZyXEL
- Kamera monitorująca Trust
- Kamera monitorująca LogiLink
- Kamera monitorująca Furrion
- Kamera monitorująca Linksys
- Kamera monitorująca Google
- Kamera monitorująca Digitus
- Kamera monitorująca Vimar
- Kamera monitorująca V-TAC
- Kamera monitorująca Dahua Technology
- Kamera monitorująca Schneider
- Kamera monitorująca Eufy
- Kamera monitorująca Ricoh
- Kamera monitorująca Emos
- Kamera monitorująca AVMATRIX
- Kamera monitorująca Renkforce
- Kamera monitorująca Rollei
- Kamera monitorująca Marshall
- Kamera monitorująca Perel
- Kamera monitorująca Somfy
- Kamera monitorująca Uniden
- Kamera monitorująca Netgear
- Kamera monitorująca Thomson
- Kamera monitorująca DiO
- Kamera monitorująca Velleman
- Kamera monitorująca Ferguson
- Kamera monitorująca DataVideo
- Kamera monitorująca Delta Dore
- Kamera monitorująca Pyle
- Kamera monitorująca Intellinet
- Kamera monitorująca CRUX
- Kamera monitorująca Setti+
- Kamera monitorująca Waeco
- Kamera monitorująca Vivotek
- Kamera monitorująca Vtech
- Kamera monitorująca Speco Technologies
- Kamera monitorująca EtiamPro
- Kamera monitorująca Edimax
- Kamera monitorująca Petcube
- Kamera monitorująca ION
- Kamera monitorująca First Alert
- Kamera monitorująca AirLive
- Kamera monitorująca Maginon
- Kamera monitorująca EnGenius
- Kamera monitorująca SPC
- Kamera monitorująca Planet
- Kamera monitorująca Brilliant
- Kamera monitorująca Genie
- Kamera monitorująca LevelOne
- Kamera monitorująca Axis
- Kamera monitorująca Sanyo
- Kamera monitorująca Lorex
- Kamera monitorująca Control4
- Kamera monitorująca Milesight
- Kamera monitorująca Aluratek
- Kamera monitorująca Abus
- Kamera monitorująca Elro
- Kamera monitorująca Olympia
- Kamera monitorująca Hama
- Kamera monitorująca Marmitek
- Kamera monitorująca Ubiquiti Networks
- Kamera monitorująca Western Digital
- Kamera monitorująca Netatmo
- Kamera monitorująca Schwaiger
- Kamera monitorująca Promise Technology
- Kamera monitorująca GVI Security
- Kamera monitorująca AVer
- Kamera monitorująca ZKTeco
- Kamera monitorująca Netis
- Kamera monitorująca Extech
- Kamera monitorująca Denver
- Kamera monitorująca Anker
- Kamera monitorująca Allnet
- Kamera monitorująca Marshall Electronics
- Kamera monitorująca Orion
- Kamera monitorująca Yale
- Kamera monitorująca SereneLife
- Kamera monitorująca Ernitec
- Kamera monitorująca AVerMedia
- Kamera monitorująca MEE Audio
- Kamera monitorująca Genius
- Kamera monitorująca Trevi
- Kamera monitorująca Technaxx
- Kamera monitorująca Atlona
- Kamera monitorująca Hanwha
- Kamera monitorująca Overmax
- Kamera monitorująca Quantum
- Kamera monitorująca Y-cam
- Kamera monitorująca Grandstream
- Kamera monitorująca Raymarine
- Kamera monitorująca Powerfix
- Kamera monitorująca Avanti
- Kamera monitorująca Ikan
- Kamera monitorująca Alecto
- Kamera monitorująca Avidsen
- Kamera monitorująca JUNG
- Kamera monitorująca Burg Wächter
- Kamera monitorująca Foscam
- Kamera monitorująca Lumens
- Kamera monitorująca Monacor
- Kamera monitorująca Dörr
- Kamera monitorująca M-e
- Kamera monitorująca EVE
- Kamera monitorująca Smartwares
- Kamera monitorująca Adj
- Kamera monitorująca Qian
- Kamera monitorująca Arenti
- Kamera monitorująca Elmo
- Kamera monitorująca Vitek
- Kamera monitorująca Alfatron
- Kamera monitorująca UniView
- Kamera monitorująca Clas Ohlson
- Kamera monitorująca Laserliner
- Kamera monitorująca Megasat
- Kamera monitorująca REVO
- Kamera monitorująca BZBGear
- Kamera monitorująca BirdDog
- Kamera monitorująca KJB Security Products
- Kamera monitorująca HiLook
- Kamera monitorująca Profile
- Kamera monitorująca Aldi
- Kamera monitorująca Aritech
- Kamera monitorująca Acti
- Kamera monitorująca ACME
- Kamera monitorująca Flamingo
- Kamera monitorująca Caliber
- Kamera monitorująca Eminent
- Kamera monitorująca Sitecom
- Kamera monitorująca Exibel
- Kamera monitorująca Fortinet
- Kamera monitorująca KlikaanKlikuit
- Kamera monitorująca Trebs
- Kamera monitorująca Ednet
- Kamera monitorująca Steren
- Kamera monitorująca Flir
- Kamera monitorująca Buffalo
- Kamera monitorująca Arlo
- Kamera monitorująca Nest
- Kamera monitorująca Siedle
- Kamera monitorująca Hive
- Kamera monitorująca Switel
- Kamera monitorująca Chacon
- Kamera monitorująca InFocus
- Kamera monitorująca Hombli
- Kamera monitorująca Naxa
- Kamera monitorująca Konig
- Kamera monitorująca Valueline
- Kamera monitorująca BRK
- Kamera monitorująca QSC
- Kamera monitorująca Xavax
- Kamera monitorująca Vaddio
- Kamera monitorująca Gira
- Kamera monitorująca Interlogix
- Kamera monitorująca Boyo
- Kamera monitorująca IC Intracom
- Kamera monitorująca Iget
- Kamera monitorująca EverFocus
- Kamera monitorująca Adesso
- Kamera monitorująca Satel
- Kamera monitorująca POSline
- Kamera monitorująca Notifier
- Kamera monitorująca Hawking Technologies
- Kamera monitorująca Friedland
- Kamera monitorująca Nexxt
- Kamera monitorująca Monoprice
- Kamera monitorująca Watec
- Kamera monitorująca Beafon
- Kamera monitorująca Chuango
- Kamera monitorująca ETiger
- Kamera monitorująca Videcon
- Kamera monitorująca INSTAR
- Kamera monitorująca Provision ISR
- Kamera monitorująca Aqara
- Kamera monitorująca Advantech
- Kamera monitorująca Digital Watchdog
- Kamera monitorująca Ganz
- Kamera monitorująca AViPAS
- Kamera monitorująca ClearOne
- Kamera monitorująca Ebode
- Kamera monitorująca Oplink
- Kamera monitorująca Sonic Alert
- Kamera monitorująca Linear PRO Access
- Kamera monitorująca Summer Infant
- Kamera monitorująca SMC
- Kamera monitorująca Topica
- Kamera monitorująca Kogan
- Kamera monitorująca Iiquu
- Kamera monitorująca Verint
- Kamera monitorująca Brinno
- Kamera monitorująca Rostra
- Kamera monitorująca Caddx
- Kamera monitorująca Spyclops
- Kamera monitorująca EKO
- Kamera monitorująca Kguard
- Kamera monitorująca Woonveilig
- Kamera monitorująca Mobi
- Kamera monitorująca Surveon
- Kamera monitorująca Hollyland
- Kamera monitorująca Epcom
- Kamera monitorująca Indexa
- Kamera monitorująca Lutec
- Kamera monitorująca Whistler
- Kamera monitorująca ClearView
- Kamera monitorująca VideoComm
- Kamera monitorująca IMILAB
- Kamera monitorująca 3xLOGIC
- Kamera monitorująca Pelco
- Kamera monitorująca Leviton
- Kamera monitorująca Inkovideo
- Kamera monitorująca Pentatech
- Kamera monitorująca Weldex
- Kamera monitorująca SecurityMan
- Kamera monitorująca Canyon
- Kamera monitorująca CNB Technology
- Kamera monitorująca Tapo
- Kamera monitorująca Aigis
- Kamera monitorująca Exacq
- Kamera monitorująca Brickcom
- Kamera monitorująca Laxihub
- Kamera monitorująca Securetech
- Kamera monitorująca EFB Elektronik
- Kamera monitorująca NetMedia
- Kamera monitorująca Videotec
- Kamera monitorująca Illustra
- Kamera monitorująca Nivian
- Kamera monitorująca E-bench
- Kamera monitorująca Syscom
- Kamera monitorująca Tecno
- Kamera monitorująca Night Owl
- Kamera monitorująca Guardzilla
- Kamera monitorująca Astak
- Kamera monitorująca Blink
- Kamera monitorująca Milestone Systems
- Kamera monitorująca Zavio
- Kamera monitorująca Campark
- Kamera monitorująca IPX
- Kamera monitorująca Dedicated Micros
- Kamera monitorująca Hamlet
- Kamera monitorująca Annke
- Kamera monitorująca AVTech
- Kamera monitorująca Qoltec
- Kamera monitorująca Approx
- Kamera monitorująca Digimerge
- Kamera monitorująca Wisenet
- Kamera monitorująca Infortrend
- Kamera monitorująca Epiphan
- Kamera monitorująca Mach Power
- Kamera monitorująca Compro
- Kamera monitorująca Aida
- Kamera monitorująca Ikegami
- Kamera monitorująca Accsoon
- Kamera monitorująca Vimtag
- Kamera monitorująca Gewiss
- Kamera monitorująca Alula
- Kamera monitorująca Insteon
- Kamera monitorująca Costar
- Kamera monitorująca ALC
- Kamera monitorująca Security Labs
- Kamera monitorująca Comtrend
- Kamera monitorująca Seneca
- Kamera monitorująca Avigilon
- Kamera monitorująca American Dynamics
- Kamera monitorująca Vosker
- Kamera monitorująca Sentry360
- Kamera monitorująca Bea-fon
- Kamera monitorująca Owltron
- Kamera monitorująca Enabot
- Kamera monitorująca Luis Energy
- Kamera monitorująca Sir Gawain
- Kamera monitorująca VisorTech
- Kamera monitorująca Atlantis Land
- Kamera monitorująca B & S Technology
- Kamera monitorująca I3International
- Kamera monitorująca IDIS
- Kamera monitorująca Ecobee
- Kamera monitorująca Conbrov
- Kamera monitorująca HuddleCamHD
- Kamera monitorująca Mobotix
- Kamera monitorująca IOIO
- Kamera monitorująca BIRDFY
- Kamera monitorująca I-PRO
- Kamera monitorująca DVDO
- Kamera monitorująca TCP
- Kamera monitorująca Bolin Technology
- Kamera monitorująca Nextech
Najnowsze instrukcje dla Kamera monitorująca

28 Stycznia 2025

25 Stycznia 2025

15 Stycznia 2025

13 Stycznia 2025

13 Stycznia 2025

13 Stycznia 2025

12 Stycznia 2025

12 Stycznia 2025

12 Stycznia 2025

11 Stycznia 2025